About Me
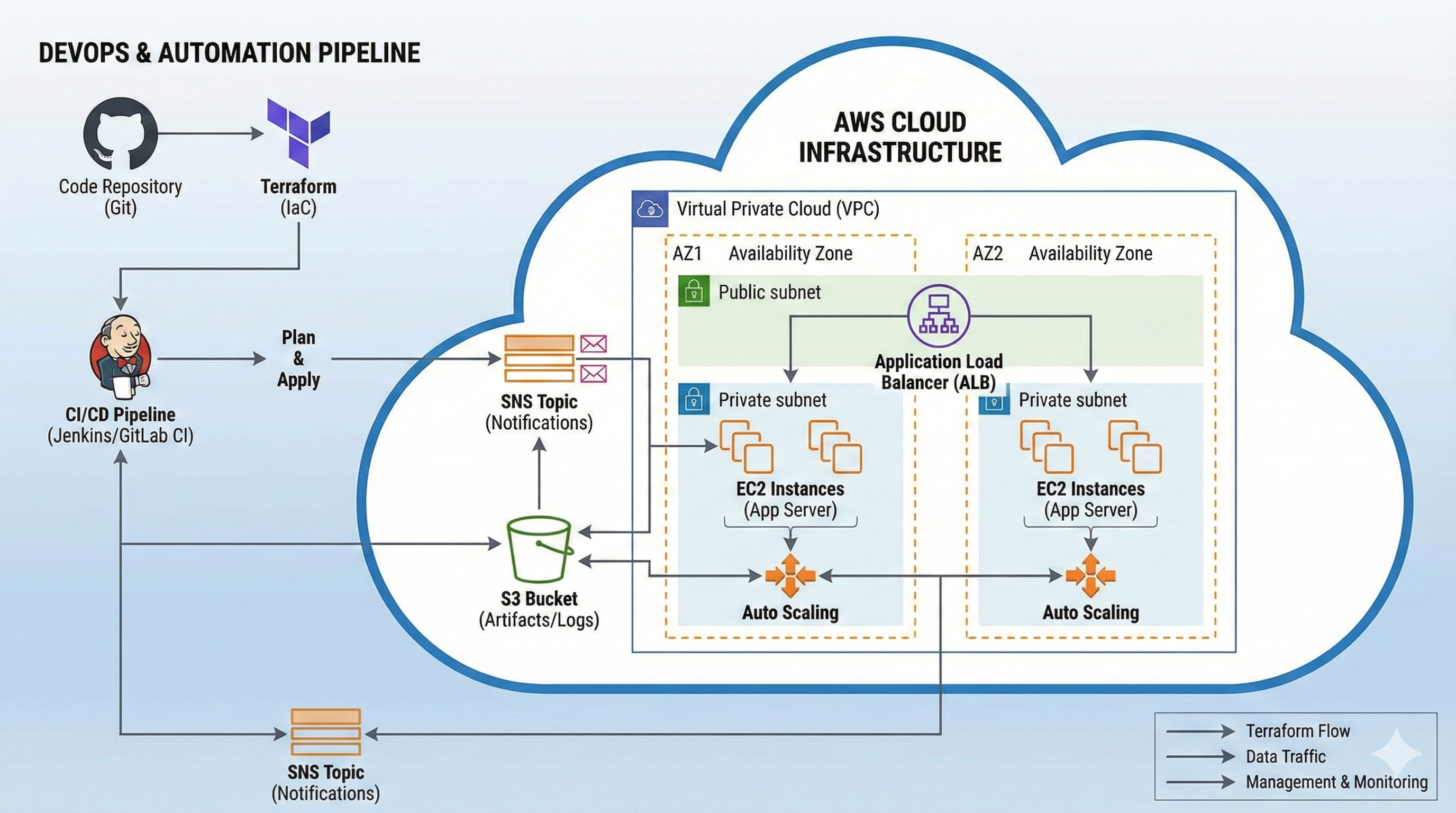
I learn Cloud & DevOps by building real-world projects on AWS and Terraform, from basic EC2 website hosting to production-ready networking with two-tier VPCs, NAT Gateways, load balancers, and event-driven architectures. My work emphasizes automation, reproducibility, and security across the full lifecycle of cloud infrastructure. (About tone partially inferred)
I focus on clear, documented workflows: plan ↠ apply ↠ validate ↠ destroy, ensuring environments are easy to spin up, test, and tear down to optimize cost and reduce operational risk. (inferred)